Installing dcrseeder
1. Introduction
dcrseeder is the Decred network aggregator, which exposes a list of trusted nodes using an internal DNS server. dcrd connects to the network’s DNS servers and searches for valid nodes. This service frequently validates known nodes and make this information available to other nodes and so on.
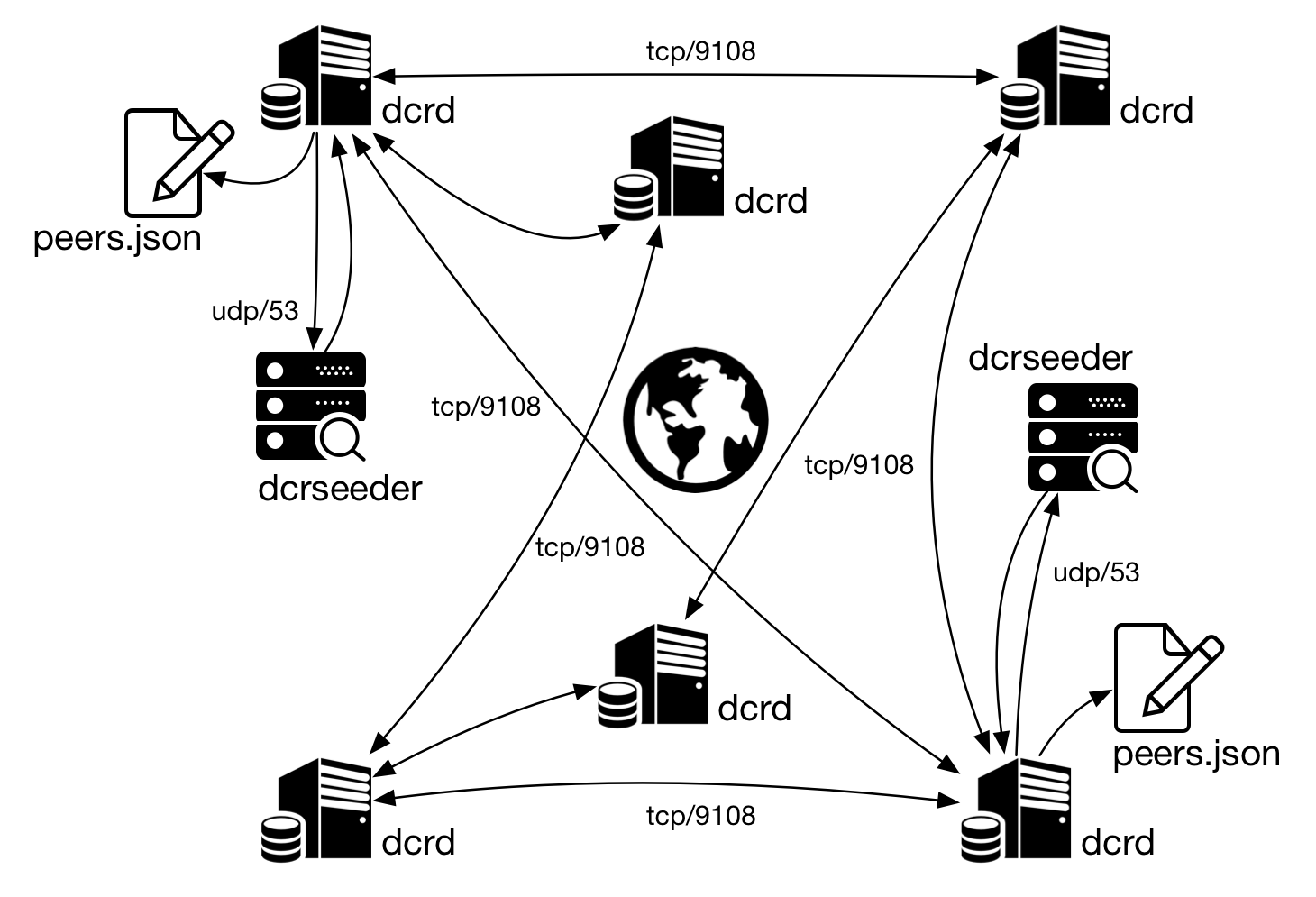
Figure 1 - dcrd queries dcrseeder to update information on nodes
To learn more, read the article The Decred structure.
Prerequisites
Go version 1.9 must be installed. To install, read the article Installation of Go (golang).
2. Installation
The following steps were performed on a Debian 9 64-bit.
a) Clone dcrseeder repository:
$ git clone https://github.com/decred/dcrseeder $HOME/go/src/github.com/decred/dcrseeder
If you do not have git installed:
$ sudo apt-get install git
b) Enter the directory you just created, run Dep to check the dependencies and compile.
$ cd $HOME/go/src/github.com/decred/dcrseeder
$ dep ensure
$ go build
or
$ /usr/local/bin/go/bin/dep ensure
$ /usr/local/bin/go/bin/go build
c) If no error occurred, a dcrseeder file with executable attribute must have been created. Try to visualize dcrseeder help message:
$ ./dcrseeder --help
d) For a permanent installation, install dcrseeder through Go:
$ go install . ./cmd/...
3. Execution
dcrd stores information about other nodes in the peers.json file, located in dcrd’s default directory, inside the network directory ( mainnet, testnet2). When searching for other nodes in the network dcrd reads this file and tries to connect to known nodes. After a while without running dcrd, it is possible that all those nodes have been turned off or their IP addresses have already changed.
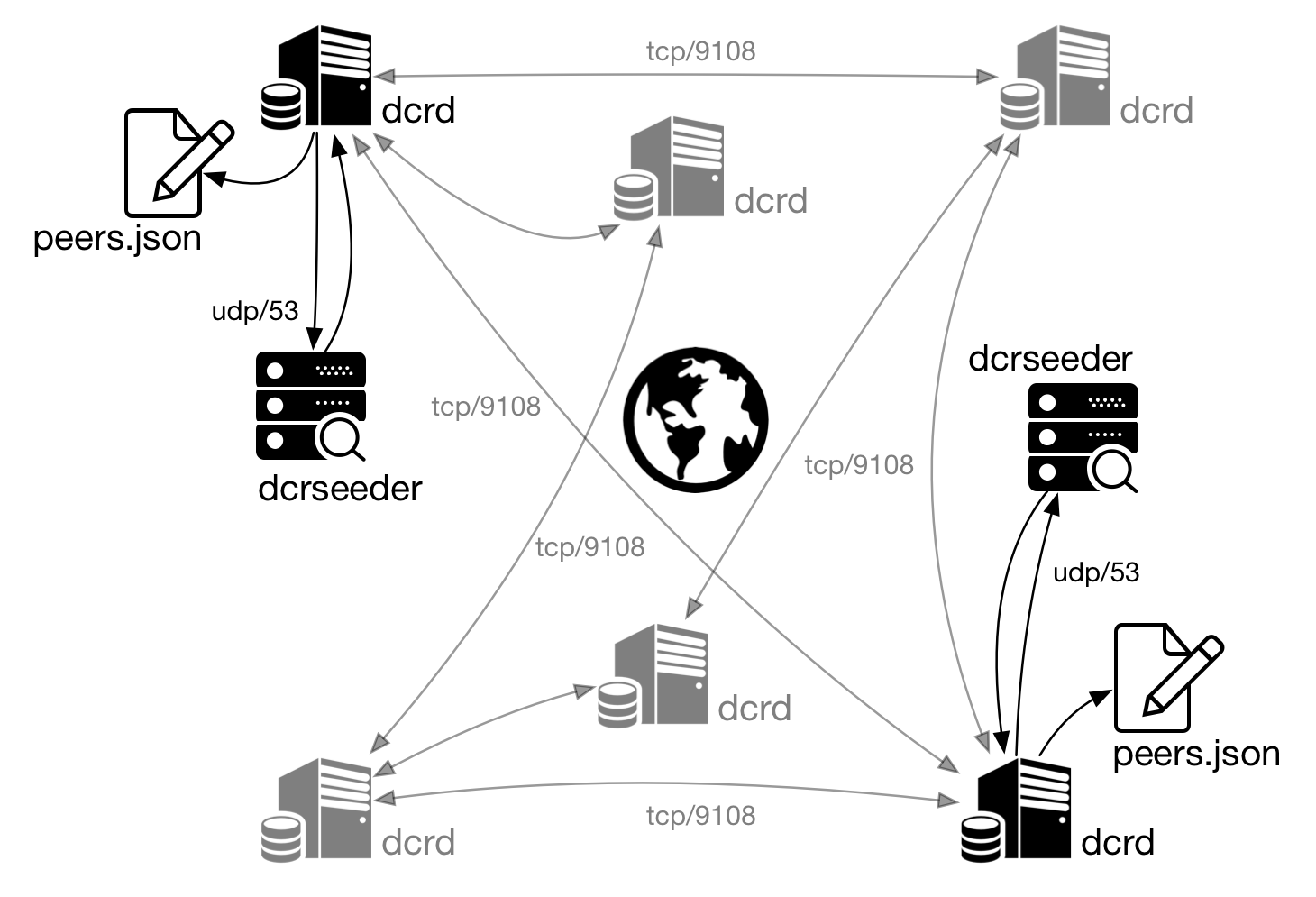
Figure 2 - dcrd uses dcrseeder to locate other nodes
To solve this issue dcrd connects to the network’s DNS servers and searches for valid nodes. This service frequently validates known nodes and make this information available to other nodes and so on.
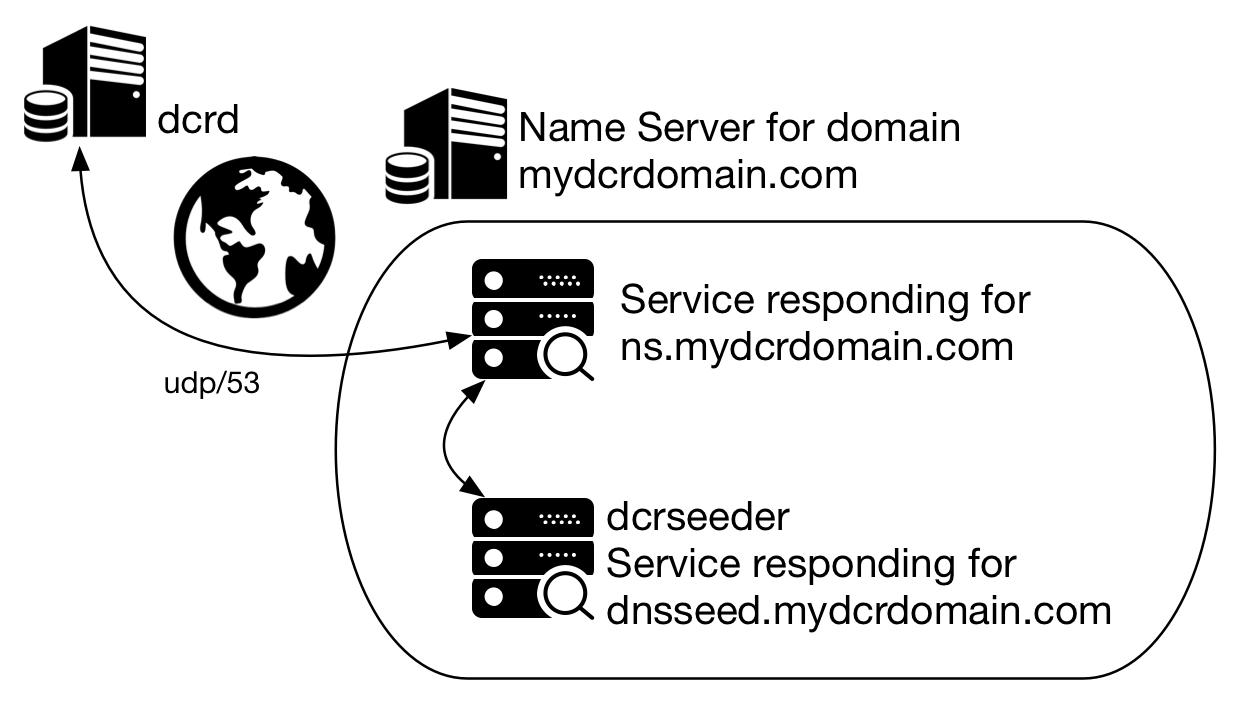
Figure 3 - A simplified DNS query scheme
DNS servers communicate using port UDP/53. To avoid using root privileges, dcrseeder is executed as a regular user and will have to listen on a non-privileged port, a port number higher than 1024, and it will be necessary to redirect UDP/53 DNS traffic to that port, such as UDP/5354, for example.
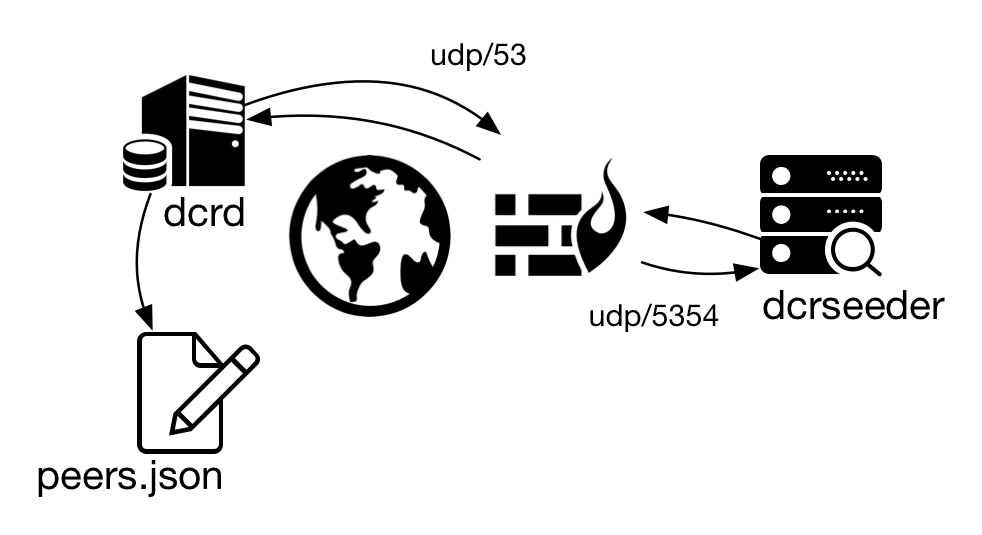
Figure 4 - PAT configured on firewall
$ sudo iptables -t nat -A PREROUTING -i $INTERFACE -p udp --dport 53 -j DNAT --to-destination 127.0.0.1:53535
Variable $INTERFACE must be replaced with the device name in the operating system (eth0, wlan0, ens33, etc.).
Besides this modification in the local firewall, you must also create a rule in your Internet router. You will have to configure at least one Network Address Translation (NAT), which is a translation of IP addresses. When a packet arrives at the public IP address for the port UDP/53, the router will forward the packet to the IP address of the server where the dcrseeder is running.
You can also configure both of these settings on the Internet router so you won’t have to configure PAT (Port Address Translation) on the local firewall. This way the packet arrives on the external interface of the Internet router on port UDP/53 and exits on the internal network to the dcrseeder on the port UDP/5354. This rule will translate IP address and port in a single configuration, also called PAT.
You will also have to create a local firewall rule to allow incoming packets to port UDP/5354:
$ sudo iptables -A INPUT -p udp --dport 5354 -m comment --comment "dcrseeder" -j ACCEPT
To run dcrseeder on port UDP/53535:
$ ./dcrseeder -H dnsseed.mydcrdomain.com -n ns.mydcrdomain.com -s 127.0.0.1
Options -H, -n and -s are mandatory:
-H <host> Hostname of the DNS seed
-n <ns> Hostname of the nameserver
-s <host> Hostname of a peer for dcrseeder
--testnet Use testnet
4. Update
To update an existing installation:
$ cd $GOPATH/src/github.com/decred/dcrseeder
$ git pull
$ dep ensure
$ go install . ./cmd/...